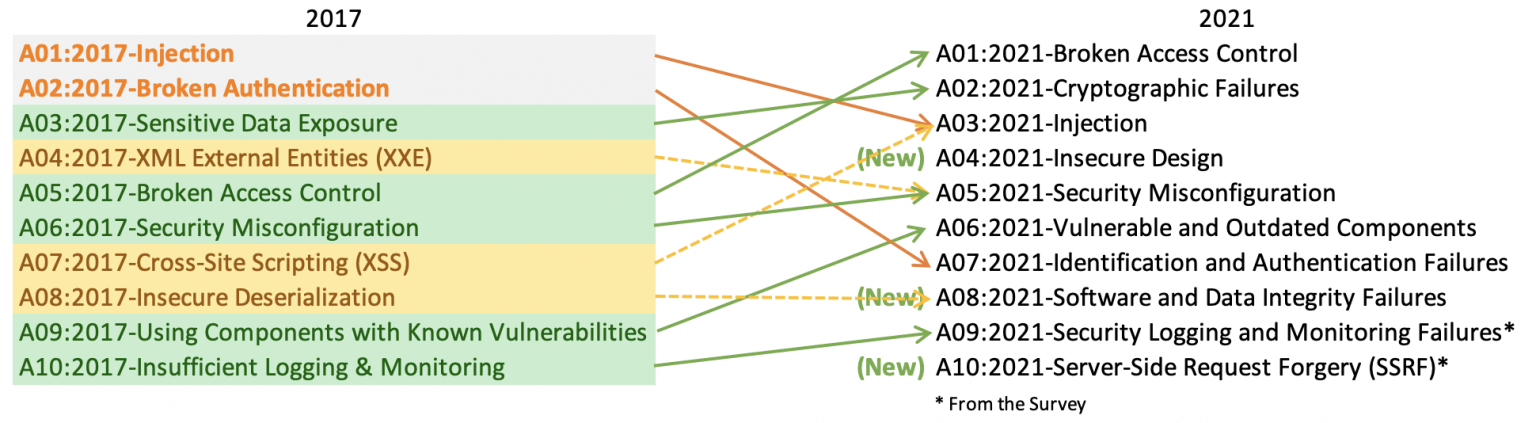
The latest installment of The OWASP Top 10 2021- a list of the most dangerous web vulnerabilities, has been updated after four years, and, after more than a decade, there is a new vulnerability at the top of the ranking.
Created in the mid-2000s, the list is curated by the Open Web Application Security Project, a nonprofit foundation that’s made up of security experts from around the world to evaluate the importance and severity of vulnerabilities in web-based apps.
For example, bug bounty platforms use the OWASP Top 10 list to classify bugs that need to be patched right away or deserve higher monetary rewards.
Because the web programming landscape and its applications are constantly evolving as new programming languages and techniques are incorporated, OWASP experts usually get together once every three-four years to update the Top 10 ranking, moving entries in or out and up and down the list to reflect the current web app ecosystem.
The ranking was updated the last time in November 2017.
But last week, the OWASP team released its upcoming list, one that comes with a complete shake-up and even a new leader.
OWASP Top 10: The full list
2021-Broken Access Control moves up from the fifth position; 94% of applications were tested for some form of broken access control. The 34 CWEs mapped to Broken Access Control had more occurrences in applications than any other category.
2021-Cryptographic Failures shift up one position to #2, previously known as Sensitive Data Exposure, which was a broad symptom rather than a root cause. The renewed focus here is on failures related to cryptography which often leads to sensitive data exposure or system compromise.
2021-Injection slides down to the third position. 94% of the applications were tested for some form of injection, and the 33 CWEs mapped into this category have the second most occurrences in applications. Cross-site Scripting is now part of this category in this edition.
2021-Insecure Design is a new category for 2021, with a focus on risks related to design flaws. If we genuinely want to “move left” as an industry, it calls for more use of threat modeling, secure design patterns and principles, and reference architectures.
2021-Security Misconfiguration moves up from #6 in the previous edition; 90% of applications were tested for some form of misconfiguration. With more shifts into highly configurable software, it’s not surprising to see this category move up. The former category for XML External Entities (XXE) is now part of this category.
2021-Vulnerable and Outdated Components was previously titled Using Components with Known Vulnerabilities and is #2 in the industry survey, but also had enough data to make the Top 10 via data analysis. This category moves up from #9 in 2017 and is a known issue that we struggle to test and assess risk. It is the only category not to have any CVEs mapped to the included CWEs, so a default exploit and impact weights of 5.0 are factored into their scores.
2021-Identification and Authentication Failures was previously Broken Authentication and is sliding down from the second position, and now include CWEs that are more related to identification failures. This category is still an integral part of the Top 10, but the increased availability of standardized frameworks seems to be helping.
2021-Software and Data Integrity Failures is a new category for 2021, focusing on making assumptions related to software updates, critical data, and CI/CD pipelines without verifying integrity. One of the highest weighted impacts from CVE/CVSS data mapped to the 10 CWEs in this category. Insecure Deserialization from 2017 is now a part of this larger category.
2021-Security Logging and Monitoring Failures was previously Insufficient Logging & Monitoring and is added from the industry survey (#3), moving up from #10 previously. This category is expanded to include more types of failures, is challenging to test for, and isn’t well represented in the CVE/CVSS data. However, failures in this category can directly impact visibility, incident alerting, and forensics.
2021-Server-Side Request Forgery is added from the industry survey (#1). The data shows a relatively low incidence rate with above average testing coverage, along with above-average ratings for Exploit and Impact potential. This category represents the scenario where the industry professionals are telling us this is important, even though it’s not illustrated in the data at this time.
2021
Broken Access Control
Cryptographic Failures
Injection
Insecure Design
Security Misconfiguration
Vulnerable and Outdated Components
Identification and Authentication Failures
Software and Data Integrity Failures
Security Logging and Monitoring Failures
Server-Side Request Forgery
2017
Injection
Broken Authentication
Sensitive Data Exposure
XML External Entities (XXE)
Broken Access Control
Security Misconfiguration
Cross-Site Scripting (XSS)
Insecure Deserialization
Using Components with Known Vulnerabilities
Insufficient Logging & Monitoring
2013
Injection
Broken Authentication and Session Management
Cross-Site Scripting (XSS)
Insecure Direct Object References
Security Misconfiguration
Sensitive Data Exposure
Missing Function Level Access Control
Cross-Site Request Forgery (CSRF)
Using Components with Known Vulnerabilities
Unvalidated Redirects and Forwards
2010
Unvalidated Redirects and Forwards
Cross-Site Scripting (XSS)
Broken Authentication and Session Management
Insecure Direct Object References
Cross-Site Request Forgery (CSRF)
Security Misconfiguration
Insecure Cryptographic Storage
Failure to Restrict URL Access
Insufficient Transport Layer Protection
Unvalidated Redirects and Forwards
2007
Cross-Site Scripting (XSS)
Injection Flaws
Malicious File Execution
Insecure Direct Object Reference
Cross-Site Request Forgery (CSRF)
Information Leakage and Improper Error Handling
Broken Authentication and Session Management
Insecure Cryptographic Storage
Insecure Communications
Failure to Restrict URL Access
2004
Unvalidated Input
Broken Access Control
Broken Authentication and Session Management
Cross Site Scripting
Buffer Overflow
Injection Flaws
Improper Error Handling
Insecure Storage
Application Denial of Service
Insecure Configuration Management
Analysis: OWASP shifts left
The 2021 ranking is also the first time since 2007 that the “Injection” vulnerability category has not been at the top of the ranking. Instead of old risks going away, OWASP has consolidated existing risks into several categories and new risks have been added, reflecting the increased threats facing web applications. For the 2021 list, OWASP added three new categories: ‘Insecure Design’,
Many of these risks are not new, so why do organizations fail to find these problems before releasing code to production, or fail to protect these vulnerabilities against attack in production? (Considering the newly added category: ‘Insecure Design’).
The impact of broken access control
- Hidden Exposure for Sensitive Data, Elevation of privilege usage of the custom API attack tool, CORS misconfiguration allowing unauthorized API access, forced browsing, and Depending on the specific vulnerability, the consequences can be devastating. The worst-case scenario is when an unauthorized user has access to a privileged function. This can give them the ability to modify or delete content on the website, or even worse, gain full control over the web application.
- Remediating of access control vulnerabilities will typically involve changes to the functionality of application code. These changes often include implementing server-side checks to ensure that the users attempting to access or modify data have rights to do so and changing the default behavior to deny access/modification unless access is explicitly granted.
- Organizations should investigate and implement a Systems Development Life Cycle (SDLC) policy that adopts secure coding practices while ensuring penetration testing is performed in the final stages of development to identify access control issues not identified during development.
What METMOX can do as your Security Specialist
- Our Cybersecurity Practitioners, Professional Services (PS), and Security Specialists, and DevOps teams can improve monitoring, compliance, and response with centralized control of all cloud workloads and IaaS, PaaS, container, and virtual environment. Our team conducts penetration testing as part of our security testing services.
- Our advanced endpoint security solution includes several technologies and capabilities like zero-day threats by using machine-learning, behavioral analysis, Security Analytics, Real-time threat intelligence, and Endpoint detection and response (EDR).
- Fully managed end-to-end vulnerability management program development and administration.
- The protection of systems and devices has become more important and we pledge to ease out the difficulty in managing your security services.
Added Benefits with Metmox
- Auditing and reporting for visibility into the usage of systems and its information
- Deliver smarter authentication, secure authorization, and high scalability
- Enforcement of user access rights to certain systems and information
- Govern and protect your business, data, users and assess
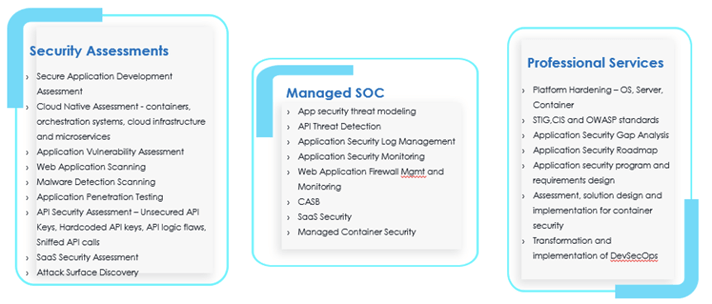
Metmox Managed AppSec services allow you to offload your application security program – from Application scanning and vulnerability validation to pen testing – onto our experts, guaranteeing a consistent application assessment process to help you to minimize your workload, maximize your productivity, and free you up for other tasks.
Metmox Application security services consist of 3 categories:
- 1. Application Security Assessments
- 2. Managed Application Security
- 3. Professional Services